Hacks Ocultos para Android, Apple e Computadores
Descubra funcionalidades ocultas e truques para melhorar sua experiência com dispositivos Android, Apple e computadores.
Blogue
Notícias recentes
-
Effortlessly Convert HEIC to JPG: A Comprehensive Guide
Switching from HEIC to JPG can be a breeze when you have the right tools and know-how. This guide will walk you through the process,…
-
Converter HEIC para JPG: Um Guia Completo em Português
Precisa converter suas fotos heic em jpg? O formato HEIC, também conhecido como HEIF (High Efficiency Image Format), é um formato de imagem moderno que…
-
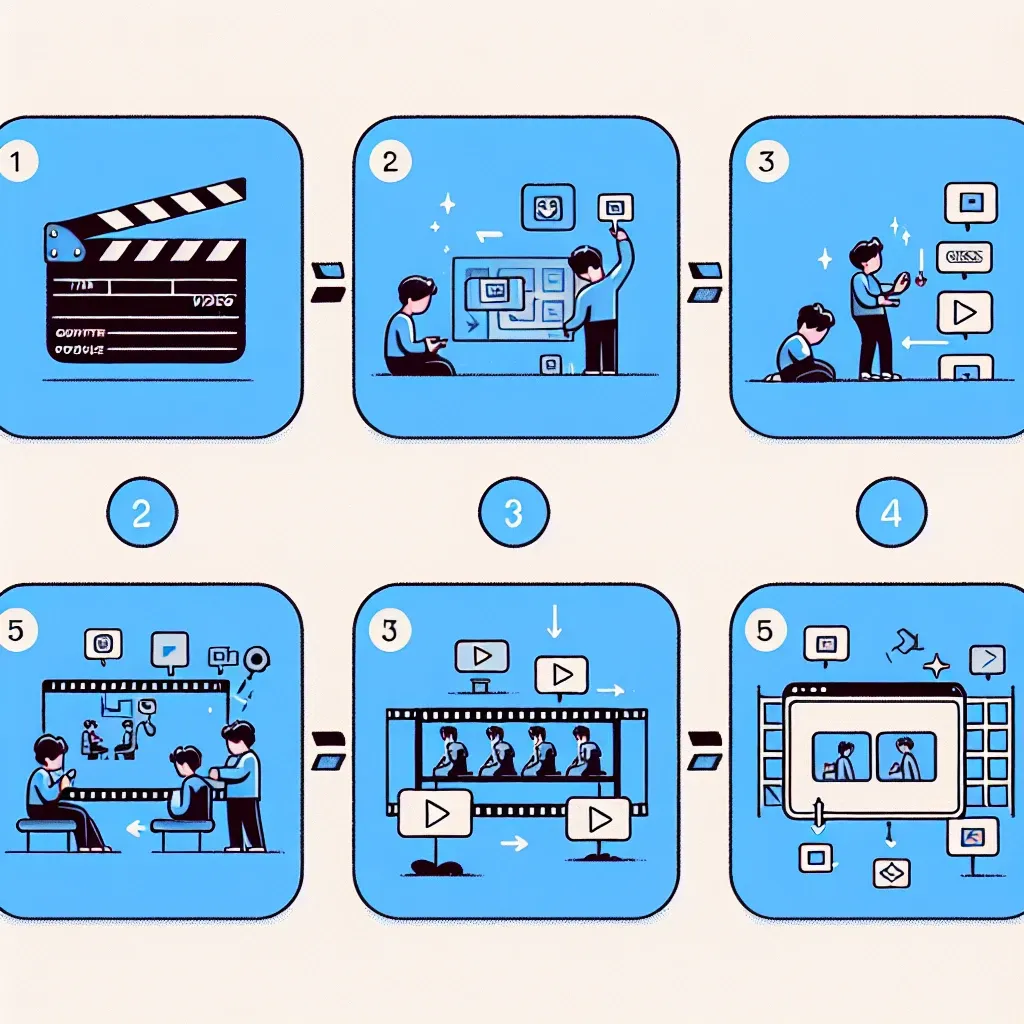
5 Easy Tricks to Make a GIF from a Video
If you’ve ever wanted to turn a video clip into a fun and shareable GIF, you’re in luck! With the right tools and a little…
-
Unleash Your Creativity: Instagram Reels Video Download Made Simple
Hey there, fellow social media enthusiasts! In today’s digital age, where content creation is king, Instagram has undoubtedly become a playground for visual storytellers. And…
-
TikTok Triumph: Unveiling the Best Video Editor for Your Creations
TikTok, the immensely popular short-form video platform, has revolutionized the way we share and consume content. With its creative tools and a vast user base,…
-
How to Set a Tiktok Video As Your Wallpaper
If you’re a TikTok enthusiast and love to personalize your device, setting a TikTok video as your wallpaper can be a great way to showcase…
-
How to Choose the Right Keyboard and Mouse
Choosing the right keyboard and mouse can significantly enhance your productivity and comfort, especially if you spend long hours at your computer. From ergonomic designs…
-
Turbine seu PC com Lifehacks inteligentes
Uma das maneiras mais impactantes de turbinar seu PC é simplificar a inicialização e gerenciar os processos em segundo plano com eficiência. Comece auditando os…
-
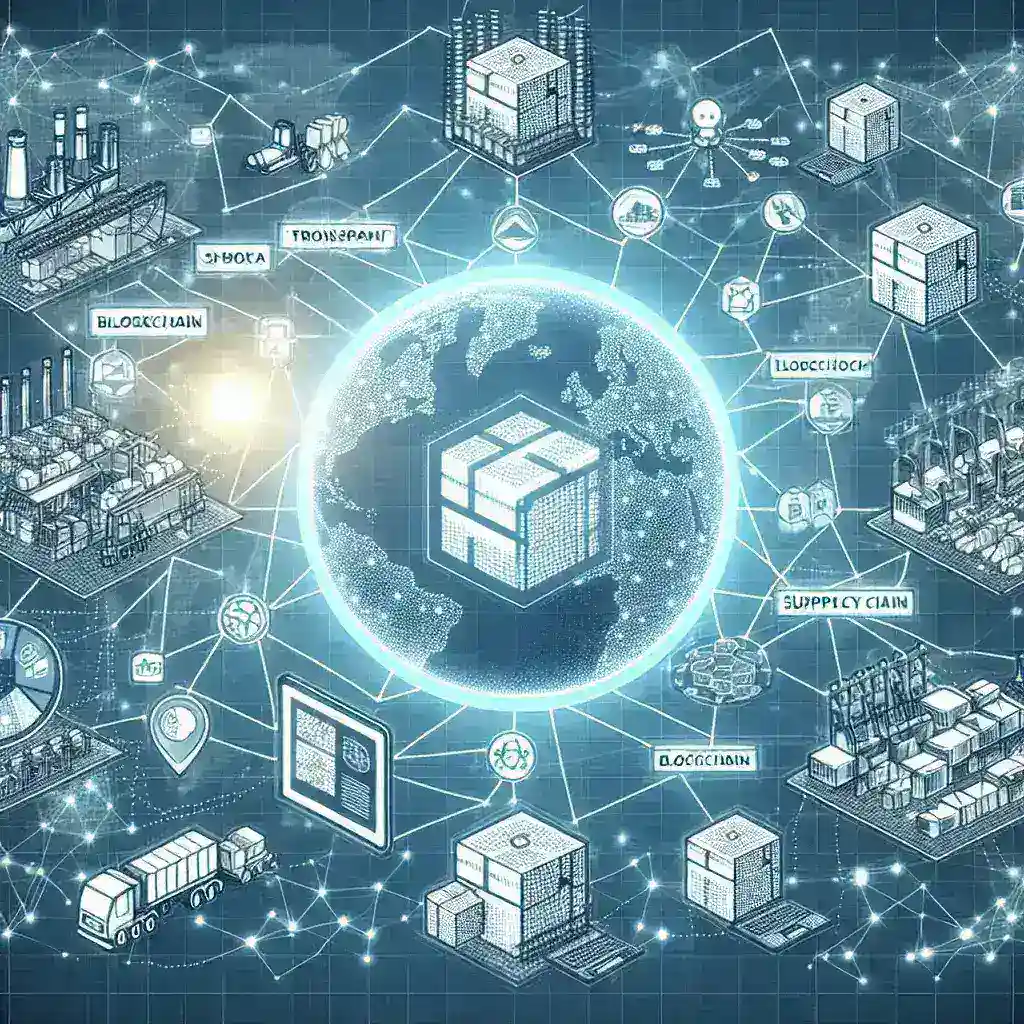
Blockchain in Transparent Supply Chains
Blockchain is a revolutionary technology that provides a secure and transparent way to store data. It operates as a decentralized ledger, ensuring that all participants…
-
How Hackers Use Malicious Updates to Infiltrate Systems
Software updates are essential for maintaining the security and functionality of computer systems. They provide patches for vulnerabilities, introduce new features, and enhance overall performance.…